Services
The Front 9: Basic Hygiene & Compliance
The Back 9: Advanced PAM & Threat Hunting

Free Environment Assessment
The "Tee Off" Every great round starts with a clear view of the course.
Patch Management
Repairing the Divots
In golf, an unrepaired divot ruins the green for everyone. In IT, unpatched software is a hole in your defense.
Basic IAM
Setting Player Handicaps
Not every player needs the same clubs.
Endpoint Protection
Your Digital Caddy
Your laptops, phones, and servers are on the front lines.
Email Security
Checking the Wind & the Lie
Phishing and malware are like unexpected gusts of wind that can ruin your drive.
Data Encryption
Locking Your Gear
If you left your clubs on the 18th green, you’d want them in a locked bag.
Backup & Recovery
The Ultimate Mulligan
Everyone wishes they had a "do-over" after a bad shot.
Security Awareness Training
The Pro-Am Clinic
The best gear in the world won't help if the player doesn't know the rules.
Perimeter Firewalls
Out-of-Bounds Markers
Your network needs clear boundaries.
Privileged Access Management (PAM)
The Master’s Jacket
High-level access is a privilege, not a right. Our PAM solution treats admin credentials like the "Green Jacket."
Session Recording
Reviewing the Film
Pro golfers analyze their swings on video; we do the same for your most sensitive accounts.
Secret Management
The Trophy Vault
API keys, certificates, and root passwords are your organization's most valuable trophies.
AI Threat Detection
The High-Tech Rangefinder
Sometimes a hazard is invisible to the naked eye.
Vulnerability Scanning
Surveying the Fairway
Course conditions change daily.
Incident Response (IR)
Calling the Course Marshal
When a rule is broken or a conflict arises, you need the Marshal.
Automated Remediation
The Sprinkler System
Why wait for a person to fix a common issue?
Red Teaming
Challenging the Pros
To be the best, you have to play the best.
Zero Trust Architecture
The Clubhouse Finish
The ultimate goal of any security program.
The Pro Shop & Management
Managed Service Provider (MSP)
The Grounds Crew & Tournament Operations
A great course doesn’t maintain itself. As your MSP, we act as a full-time operations team, handling the day-to-day “mowing and watering” of your IT environment. We ensure your systems are up, your hardware is healthy, and the technical infrastructure is ready for play every single morning.
Benefit: Offloads the complex burden of IT management, so your leadership can focus entirely on business growth.
Multi-Factor Authentication (MFA)
The Double-Gate Entry
Even with a membership card, the most secure clubs require a second form of ID. MFA adds that critical second layer—a code, a push notification, or a physical key—ensuring that even if a “bad actor” steals a password, they still can’t get past the gate.
Benefit: Blocks over 99.9% of account compromise attacks by requiring a second, physical proof of identity.
Advisory Services
The Club Pro & Strategic Consultant
Sometimes you need more than just gear; you need a strategy to win the tournament. Our Advisory Services provide executive-level guidance, from compliance roadmaps to virtual CISO (vCISO) leadership, helping you navigate complex regulatory “water hazards” and long-term security planning.
Benefit: Provides expert, high-level security leadership without the overhead cost of a full-time executive hire.
Identity Management
The Official Player Registry
Every person on the course needs to be accounted for. Identity Management is the centralized system that tracks every “player” in your organization from the moment they are hired (onboarding) to the moment they retire (offboarding), ensuring their access is always accurate and up-to-date.
Benefit: Streamlines the hiring and firing process while ensuring former employees are instantly and completely removed from your systems.
A LA Cart Services
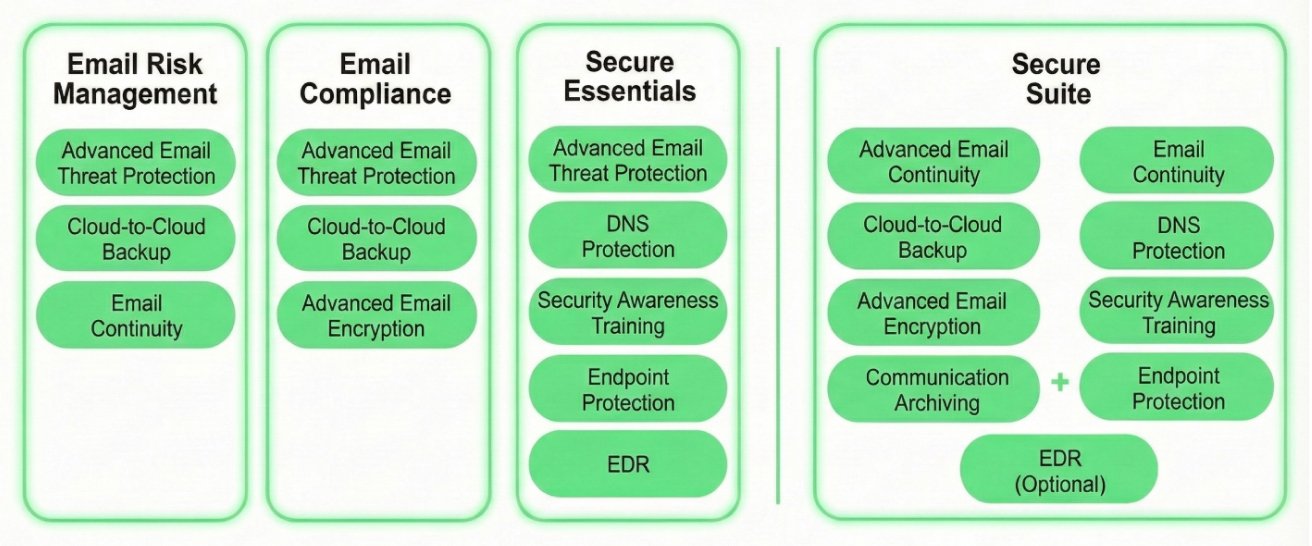
Email Risk Management & Compliance
Secure Essentials & Secure Suite
Endpoint Protection
The Play (The "Digital Caddy"): Real-time monitoring of laptops, desktops, and servers to detect and block threats using behavioral analysis.
Technical Details: A lightweight agent that uses machine learning—not just signatures—to stop zero-day attacks and ransomware before they can breach the perimeter.

DNS Protection
The Play (The "Fairway Markers"): A network-level firewall that blocks access to malicious domains and prevents data from being "sharked" out of your network.
Technical Details: Filters DNS requests for all processes to block communication with Command & Control (C&C) servers. It leverages real-time threat intelligence to reduce malware incidents by up to 27%.

Security Awareness Training
The Play (The "Pro-Am Clinic"): Continuous education that teaches employees how to identify scams and avoid risky digital behaviors.
Technical Details: Includes a phishing simulator with real-world templates and a Learning Management System (LMS) to track progress and ROI.

EDR
The Play (The "Course Marshal"): Advanced monitoring that allows for rapid "on-course" incident response and forensic investigation.
Technical Details: Provides deep visibility into endpoint activity, allowing admins to isolate infected devices, kill malicious processes, and perform root-cause analysis.

