Compliance Checklist
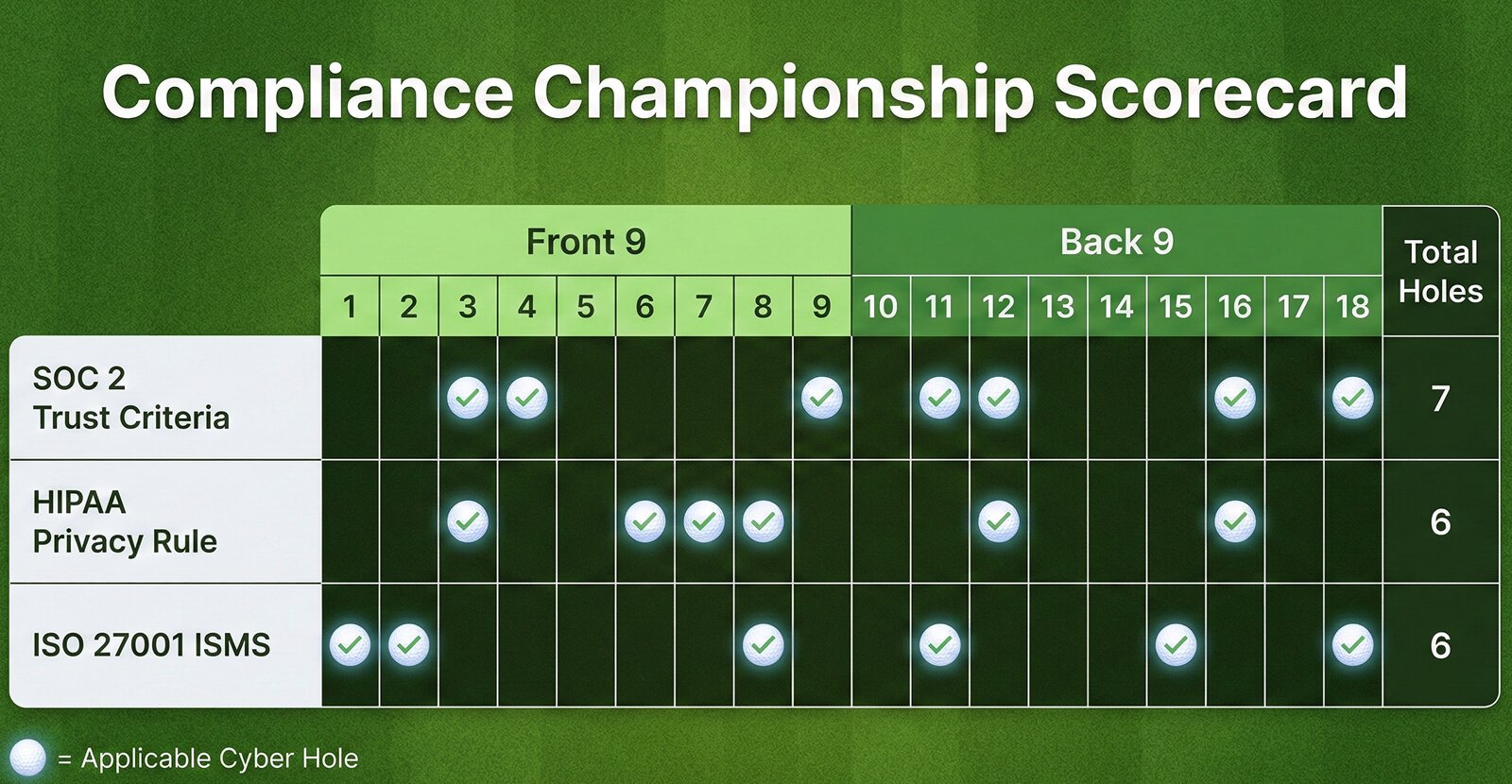
Checklists [SOC 2, HIPAA, ISO 27001]
1. SOC 2 Compliance Checklist
SOC 2 focuses on the Trust Services Criteria — Security (mandatory), Availability, Confidentiality, Processing Integrity, and Privacy. (The HIPAA Journal)
Scope & Planning
- Define the SOC 2 scope (systems, data, services). (ISMS.online)
- Choose applicable Trust Services Criteria (Security mandatory; others as needed). (ISMS.online)
- Assign compliance roles & responsibilities. (Hicomply)
Policies & Documentation
- Information security policy suite (access control, incident response, change management). (Hicomply)
- Data classification & handling procedures. (Hicomply)
- Privacy and confidentiality policies. (The HIPAA Journal)
Risk & Access Controls
- Perform a formal risk assessment and risk treatment plan. (DSALTA)
- Implement logical and physical access controls (MFA, RBAC, principle of least privilege). (Compliancy Group)
- Quarterly access reviews and recertification. (Compliancy Group)
Technical Security
- Network firewalls, IDS/IPS, and SIEM monitoring. (Compliancy Group)
- Encryption of data at rest and in transit. (The HIPAA Journal)
- Vulnerability scanning and penetration tests.
Availability & Monitoring
- System performance and availability monitoring. (The HIPAA Journal)
- Backups with documented recovery testing. (DSALTA)
- Incident detection log aggregation. (Compliancy Group)
Incident Response & Business Continuity
Third-Party & Vendor Risk
- Vendor inventory with contract and security requirements. (DSALTA)
- Annual or risk-based third-party security assessments.
Audit Preparation
2. HIPAA Compliance Checklist
HIPAA compliance applies if your site handles Protected Health Information (PHI). It is centered on Administrative, Technical, and Physical Safeguards.
Administrative Safeguards
- HIPAA policies & procedures (privacy, security, breach notification).
- Assigned security/privacy officers.
- Workforce training on HIPAA rules and PHI handling.
- Risk assessment and risk management plan.
- Documentation of risk analysis and mitigation.
- Sanction policy for workforce non-compliance.
Technical Safeguards
- Access controls (unique user IDs, MFA, session timeout).
- Encryption for PHI in transit and at rest. (DSALTA)
- Automatic log-off procedures.
- Audit controls (log review, monitoring systems).
- Integrity controls (checksums, hashes, versioning).
Physical Safeguards
- Facility access controls (badges, locks).
- Workstation use and security standards.
- Device and media controls for hardware that stores PHI.
Breach & Incident Response
- HIPAA-specific breach response plan.
- Notification procedures within HHS timelines.
Business Associate Agreements
- Signed agreements (BAAs) with vendors handling PHI.
3. ISO 27001 Compliance Checklist
ISO 27001 is a formal Information Security Management System (ISMS) certification with structured documentation and audit requirements. (DSALTA)
ISMS Foundation
- Establish ISMS scope and objectives aligned with business.
- Executive leadership commitment and governance.
Risk Management
Policies & Procedures
- Information security policies approved and published.
- Asset management procedures.
- Acceptable use and data classification policies.
Control Implementation (Annex A Controls)
ISO 27001 includes ~90 controls across Annex A domains. Examples:
Training & Awareness
- Security awareness training records. (DSALTA)
Internal Audit & Review
Continuous Improvement
- Monitor control effectiveness.
- Update risk treatments and SoA annually.
Tips for Combined Compliance
Since these frameworks overlap (e.g., access control, logging, incident response), you can standardize common controls and evidence to satisfy all three rather than duplicating effort. (DSALTA)
Examples Of Overlaps:
If you want, I can turn this into a customized Excel/CSV audit checklist or tie it to your specific tech stack and threat model.

